When the VShell server and shared resources are running in a properly configured Windows Active Directory domain, file shares can be made available to accounts that authenticate using public keys. This page includes all the steps necessary to configure the domain and VShell server. Access to file shares applies to all SSH2 clients, including SecureFX, SecureCRT, and the sfxcl.exe, vsftp.exe, and vcp.exe command-line utilities.
VShell supports a Windows capability called Kerberos Protocol Transition (KPT), which is part of the infrastructure created by Microsoft to support Kerberos. The VShell server takes advantage of Windows KPT to create the user's credentials, but does not use Kerberos authentication.
Configuration occurs largely on the domain controller, where the administrator sets up constrained delegation for the systems that will handle authentication requests.
VShell configuration simply consists of enabling the Kerberos Protocol Transition option.
In order to support Windows file shares via Kerberos Protocol Transition, the Windows environment must meet the following conditions:
In this procedure, the following example environment is used:
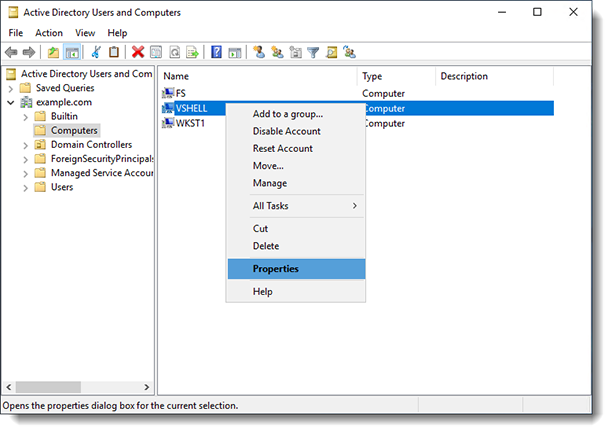
To configure constrained delegation, log onto dc.example.com as a domain administrator and launch the Active Directory Users and Computers MMC interface (open the Start menu and select Administrative Tools):
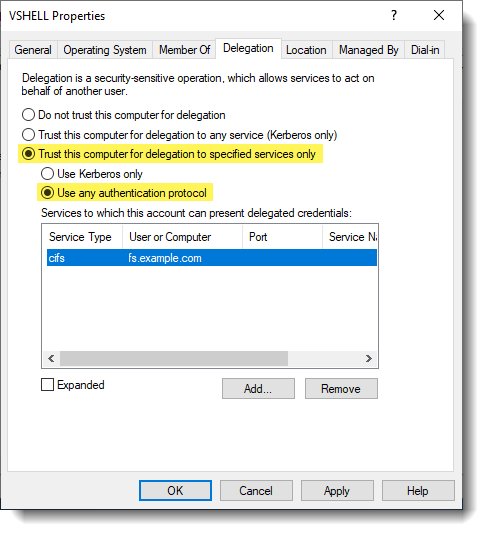
Important: VShell virtual root paths to the network file share must use the fully qualified domain name (FQDN) of the targeted file server (fs.example.com), since that is what has been specified for delegation. Using the non-qualified hostname may not allow sufficient permissions for VShell users to access the file server.
VShell Server 3.6 and later on vshell.example.com
VShell Server 2.6.3 – 3.5.4 on vshell.example.com
WARNING: If you use the registry editor incorrectly, you may cause serious problems that may require you to reinstall your operating system. There is no guarantee that you can solve problems that result from using the registry editor incorrectly. Use the registry editor at your own risk.
HKEY_LOCAL_MACHINE\SOFTWARE\VanDyke\VShell\Server
With the VShell server and the Active Directory domain controller configured properly as described above, users should be able to authenticate to VShell on vshell.example.com using public-key-only authentication and gain access to the share "fileshare" on fs.example.com.
VanDyke Software uses cookies to give you the best online experience. Before continuing to use this site, please confirm that you agree to our use of cookies. Please see our Cookie Usage for details.
Here you can control cookies using the checkboxes below. Some cookies are essential for the use of our website and cannot be disabled. Others provide a convenience to the user and, if disabled, may reduce the ease of use of our site. Finally, some cookies provide anonymous analytic tracking data that help us provide the user with a richer browsing experience. You can elect to disable these cookies as well.